Kemp Security Series 2020 – Part 2: SSL/TLS Security

The 2019 Trustwave Global Security report is an annual snapshot of the threats faced by web-based applications and services. The 2019 report, which is based on data collected in 2018, highlights and discusses many such threats. In a previous article in this series, we looked at Application security. In this post we will focus on how enforcing organizational wide standards and use for SSL/TLS encryption can help secure your Internet facing services.
Encryption of data within SSL/TLS based systems is an important part of all network and application protection schemes. Attacks against such security systems were the most common in the latest report, with 4 of the top 5 network vulnerabilities detected being SSL or TLS related. The Trustwave report shows that attacks against out of date or poorly configured SSL/TLS systems are also increasing, making it vital that these systems are deployed correctly and kept up to date. However, correctly configuring these network security systems, and keeping them up to date, is time-consuming and often tricky.
SSL/TLS Security With Kemp
LoadMaster can also be the central hub of your network for handling SSL/TLS encryption. Handling SSL/TLS encryption for network packets is a resource intensive task. Doing this on the web servers and application servers that are there to serve client requests puts an additional overhead on servers that should be optimized for content delivery. A LoadMaster application delivery controller can be configured as an SSL Accelerator. When performing this role, the LoadMaster is optimized to quickly perform SSL and TLS decryption and encryption for incoming and outgoing network traffic.
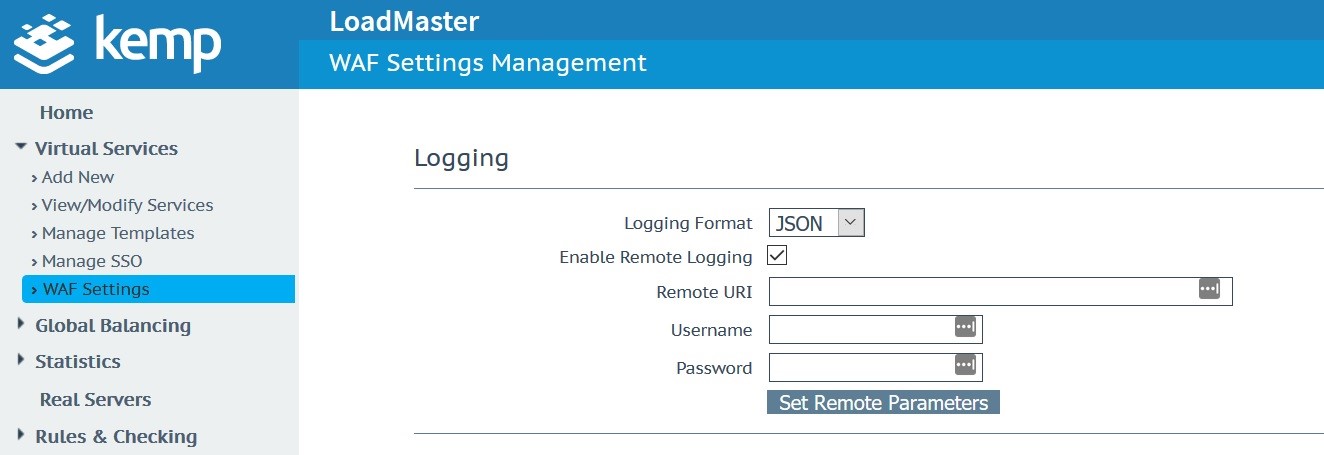
In addition to removing the burden of the SSL/TLS encryption from back-end servers, LoadMaster also helps reduce the burden of correctly configuring SSL/TLS for network administrators. The LoadMaster Web User Interface (WUI) makes it easy to configure SSL and TLS settings correctly (as shown in Figure 1 below). The default settings are per the Trustwave guides for PCI DSS compliance that SSL 3.0 and TLS 1.0 protocols should be disabled by default.
Specific features include:
- Decrypt and Re-Encrypt
- Full Certificate management incl.:
- Client certificates
- Importing and maintaining certificates
- OCSP Support
- SNI Support
- Full Cipher Suite management incl.:
- Default best practices to support A-rated Qualys scan
- Pre-configured cipher suites including FIPS, ECDSA_Default, ECDSA_BestPractices and more
- Ability to create and tailor your own cipher suite for your application
- Ability to apply this to both the data plane and to control and specify access to the LoadMaster
The LoadMaster SSL/TLS implementation is also kept up to date with current industry best practice and tested against sites such as Qualys SSL Labs. The results of these tests can be made available to interested customers. Moving SSL/TLS handling to Loadmaster also allows legacy applications that may not support up to date SSL/TLS versions to be protected behind a modern secure load balancer.
The Trustwave report shows that proper SSL/TLS implementation, configuration, and management is important. Vulnerabilities in this part of an Internet-facing infrastructure are increasingly the target for malicious 3rd parties.
Contact us today to discuss all your application delivery and security needs.
Additional Information Trustwave 2019 Global Security Report Verizon 2019 Data Breach Investigations Report

David O'Connor
David O’Connor is a Product Manager in Kemp working in Limerick, Ireland. He holds a bachelor’s degree in Computer Engineering from University of Limerick. David has a telecoms background with previous roles in development, customer support and presales with a focus on product-market fit and creating tech products that customers love.
more from the author