LoadMaster 360 - Simplifying Your LoadMaster Management

Applications play a crucial role in most IT-related tasks that involve users. At the end of any business process, people will likely be using applications. These applications can be web apps in a browser, mobile apps on smartphones or tablets, or traditional desktop or centralized database-backed business applications. Most applications now get delivered over the internet, frequently through thin-client wrappers to allow the web-enabling of legacy business apps.
The growing popularity of the hybrid work model in recent years has made it more difficult for IT teams to provide a seamless application experience for all users, regardless of their work location. The application experience has become vital to IT service delivery. At Progress, we understand this and provide tools to help organizations deliver a premium experience to their employees and customers.
Progress LoadMaster 360 Overview
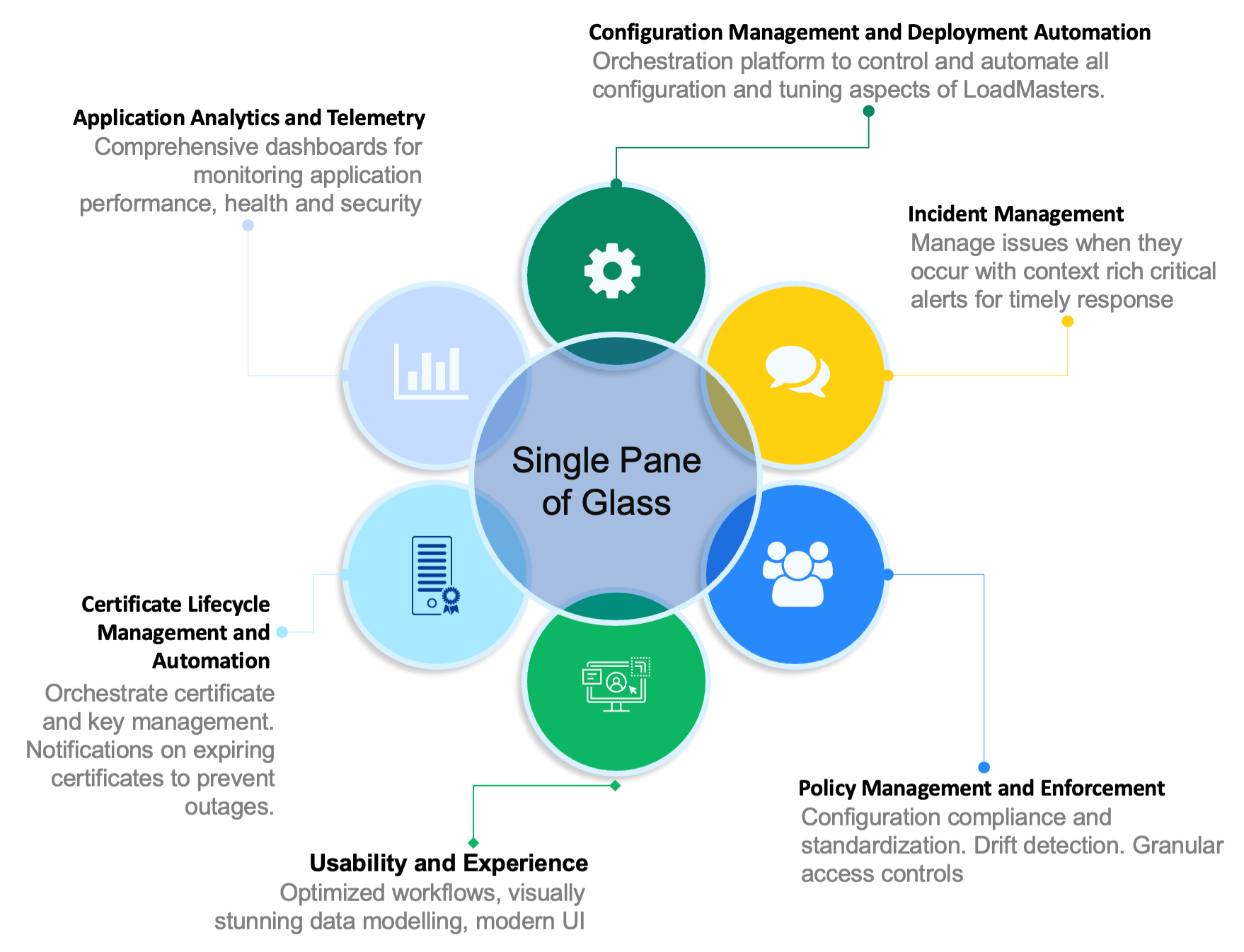
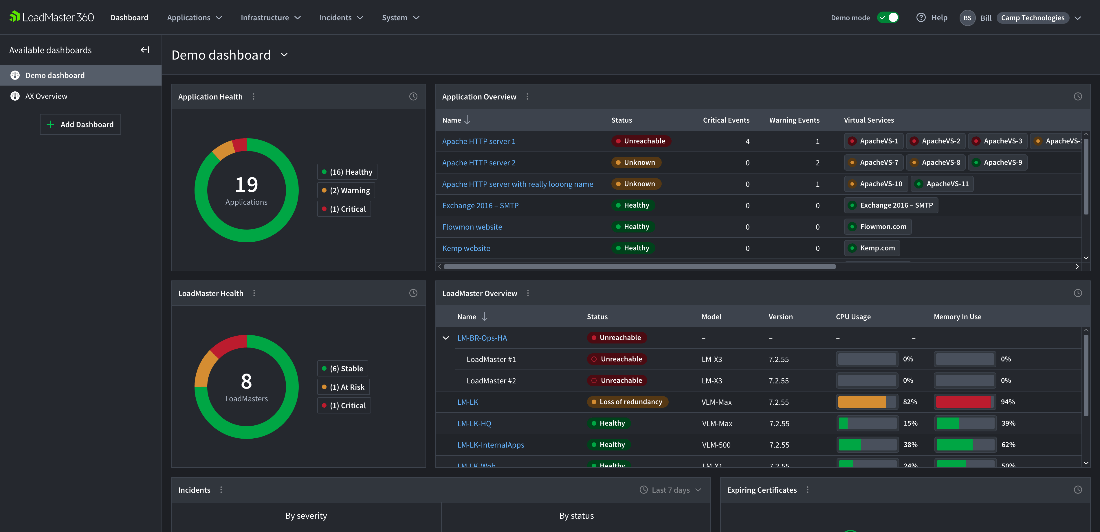
LoadMaster 360 is a single pane of glass experience that makes it easier for application, network and security teams to maintain application availability, performance and security. LoadMaster 360 is a SaaS solution providing enhanced capabilities, insights and management free updates.
Current Network Management Market Expectations
Feedback from our existing LoadMaster client base and broader industry data shows that system administrators and the organizations they work for expect application management platforms to deliver the following:
- Centralized management of application delivery across all platforms
- Contextualized Insights and Analytics
- Excellent user interface – across visualizations and workflows
- Flexible license models
We couldn't agree more. We would add that the interface for the application management platform should be intuitive and provide relevant information at each moment. LoadMaster 360 currently delivers or will soon deliver information in the six core pillars shown in Figure 1.
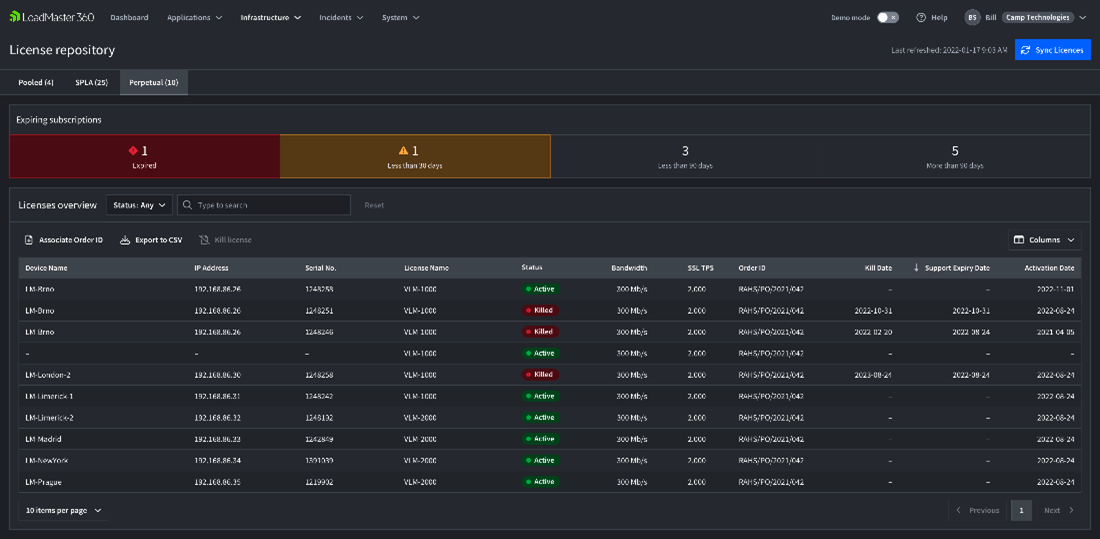
LoadMaster 360 is a cloud service that operates securely through connectors to manage LoadMaster devices anywhere. It supports multiple sites to cater to multi-cloud and hybrid-cloud environments. We also provide License Management capabilities to enable our users to be more flexible with how you deploy and use LoadMaster(s) in your estate. This allows licensing on-demand of LoadMaster instances when needed and the recovery of the license for reuse when LoadMaster instances get decommissioned.
See What LoadMaster 360 Can Do
The Benefits of Loadmaster 360
After deploying LoadMaster 360 to manage on-premise, cloud, or hybrid LoadMaster instances, organizations will experience the following benefits:
- Easier management of LoadMaster instances - helping to make your business infrastructure dynamic and more robust to changing loads and conditions.
- The surfacing of deep insights into how applications perform individually and as part of the broader business operational landscape.
- Real-time alerting of issues or trending concerns that will impact the user experience, allowing you to take immediate steps to address the issue.
- An intuitive visual representation of the application delivery infrastructure that is both system admin and non-technical management friendly.
- Simplifying and eliminating common issues that can lead to downtime - such as streamlining certificate awareness and usage for your critical applications.
- Easier adoption of many powerful features of LoadMaster that organizations may not have yet been using (e.g., our Edge Security Pack and Web Application Firewall feature sets).
Example Use Cases
Adopting LoadMaster 360 will confer additional benefits based on the use cases of each organization. Some typical use cases include:
Manage Hybrid & Multi-Cloud Application Delivery
Organizations manage many applications across various on-premise and cloud platforms. However, each platform has unique tools to provision, configure and manage application delivery. As a result, organizations face several challenges, including the need for staff to possess skillsets across multiple toolsets, the difficulty in maintaining visibility across the different tools and processes used to surface and address issues, and the absence of a single source of truth for conducting root cause analysis across the entire infrastructure.
LoadMaster 360 streamlines your workflow into one interface that manages your LoadMaster across all platforms. The interface unifies app configuration and device management, allowing for consistent policy control. Additionally, LoadMaster 360 is designed to work for all teams, including app support, network and cybersecurity, providing sharable insights.
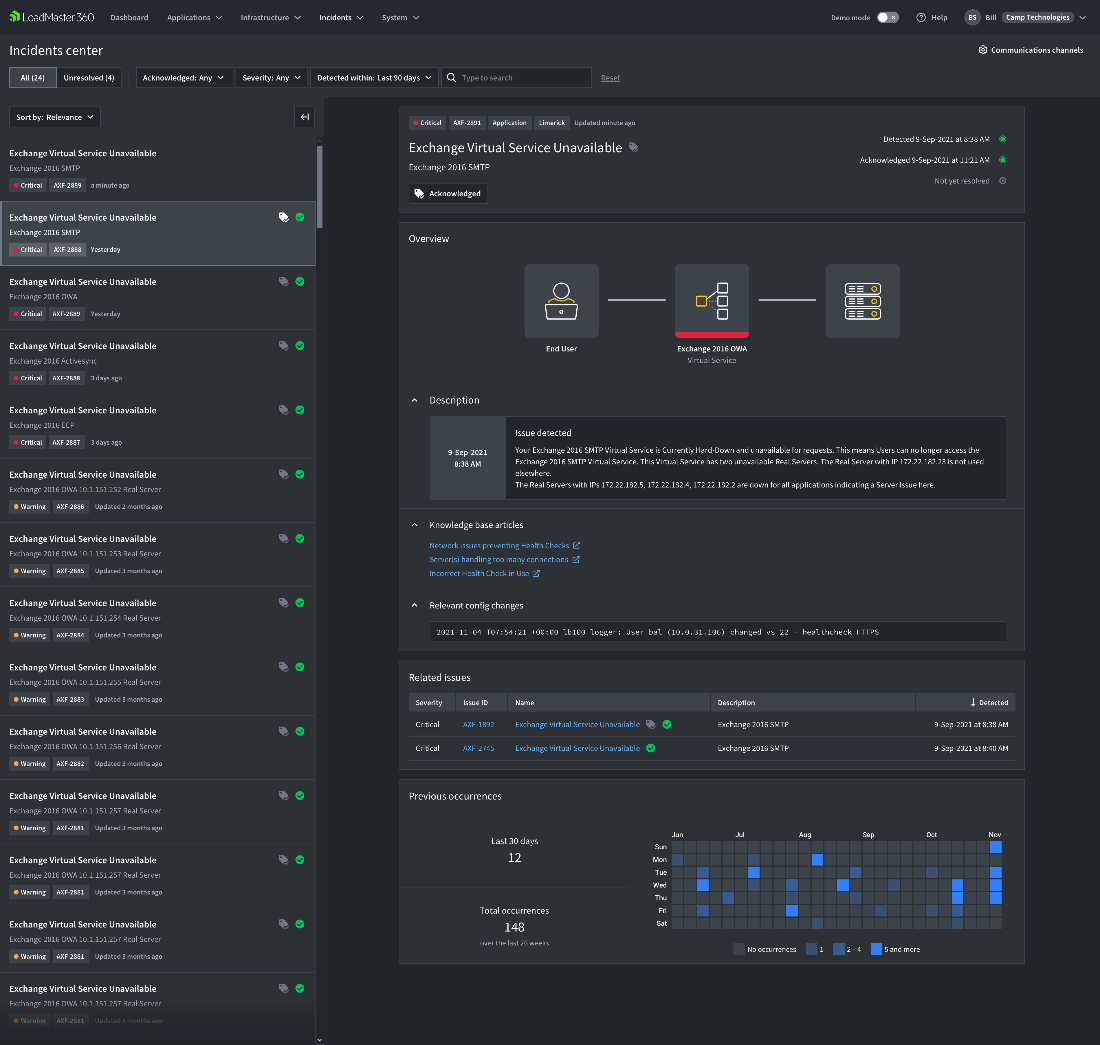
Multi-Team Incident Management
When faced with an application delivery issue, there are various obstacles to overcome, including promptly identifying the problem and directing it to the appropriate team, notifying management, determining the root cause, and effectively communicating across teams with differing perspectives. This can be a challenge. LoadMaster 360 addresses this challenge by providing in-context analysis and guidance that reduces mean time to resolution.
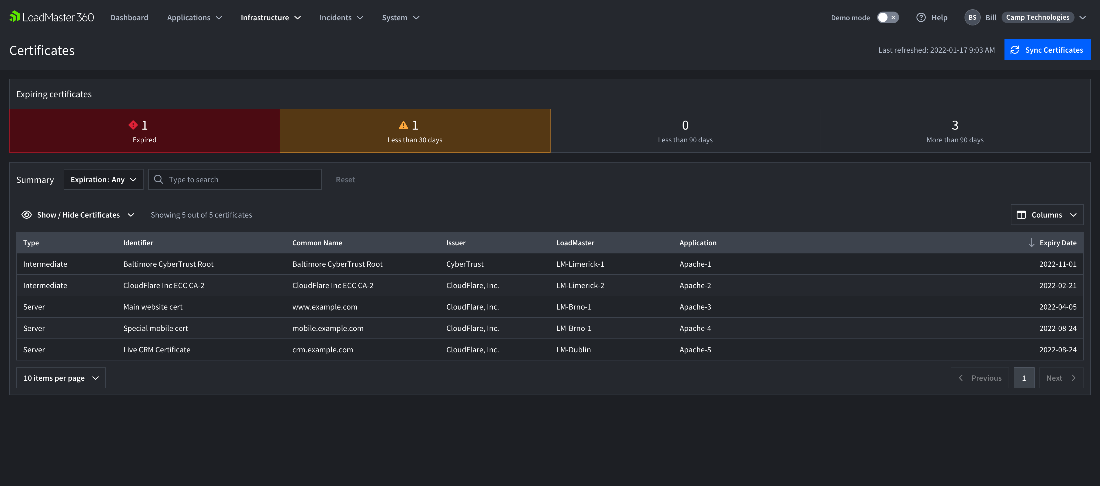
Certificate Management
In the world of web applications, certificates play a crucial role. They are responsible for ensuring security, and if they expire, users will encounter security errors that could potentially harm the business's reputation and make the application unusable.
The latest cybersecurity best practice advice is pressuring the market to use certificates with shorter expiration windows spanning months rather than years. This means that certificates need to be updated more often, and there is an increased risk that an update for one will be missed. LoadMaster 360 currently allows users to observe all certificates and alerts them to upcoming expiration dates.
Licensing & Capacity Management
Coming Soon with LoadMaster 360
Now that we’ve launched LoadMaster 360, we can begin to add additional planned functionality. User can expect these features:
- Policy Management and Enforcement – Configuration compliance and standardization, drift detection and granular access controls.
- Configuration Management and Deployment Automation – Control and automate all LoadMaster configuration and tuning aspects with this orchestration platform.
- Certificate Automation and Renewal – Handling the certificate lifecycle with automated issuance and renewal of critical certificates through your current CA’s.
How You Can Learn More
LoadMaster 360 will revolutionize deploying, configuring and managing your LoadMaster estate, and enable you to deliver the best experience for your users and clients.

Doug Barney
Doug Barney was the founding editor of Redmond Magazine, Redmond Channel Partner, Redmond Developer News and Virtualization Review. Doug has also served as Executive Editor of Network World, Editor in Chief of AmigaWorld and Editor in Chief of Network Computing.
more from the author