As new features are added to the public cloud, we need to continuously re-analyze the products we use to see what we are able to take advantage of. Recently, Microsoft announced the preview of Azure Active Directory Domain Services. With AAD Domain Service, now you can do things like add virtual machines running in the Infrastructure as a Service (IaaS) to an Active Directory domain without having to spin up domain controllers. Not to mention leverage Group Policy to centralize management of your virtual server infrastructure. Additions like these are a big move to providing the feature rich environment we expect in the public cloud.
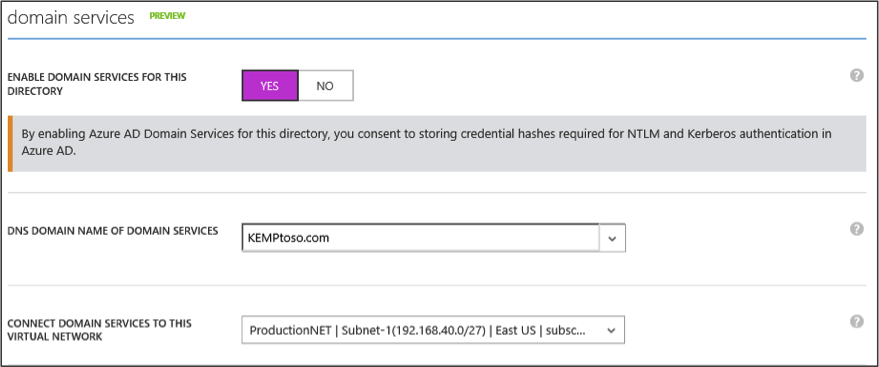
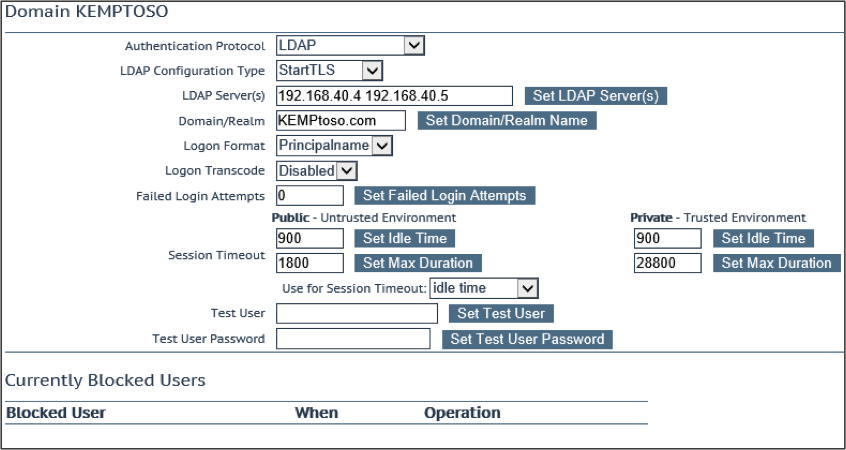
When setting up Azure Active Directory Domain Services, you must select a virtual network in which to connect it to. Once the activation of Domain Services is complete, you are provided with 2 IP addresses within the virtual network you selected. These IP addresses can be used as DNS servers in the network card settings for your virtual machines as well as for third party solutions when pre-authentication is being leveraged
KEMP’s Virtual LoadMaster Edge Security Pack (ESP) is a solution that provides secure application publishing, Single Sign On, application integration, and flexible authentication options. ESP was originally released as a replacement for Microsoft Threat Management Gateway and had quickly become a must have for KEMP customers. The Edge Security Pack has evolved over the years with new features and functionality to adapt to customer requirements. Some of the more recent enhancements are:
- Nested permitted Active Directory groups
- Active Directory Group traffic steering
- Multi-domain authentication
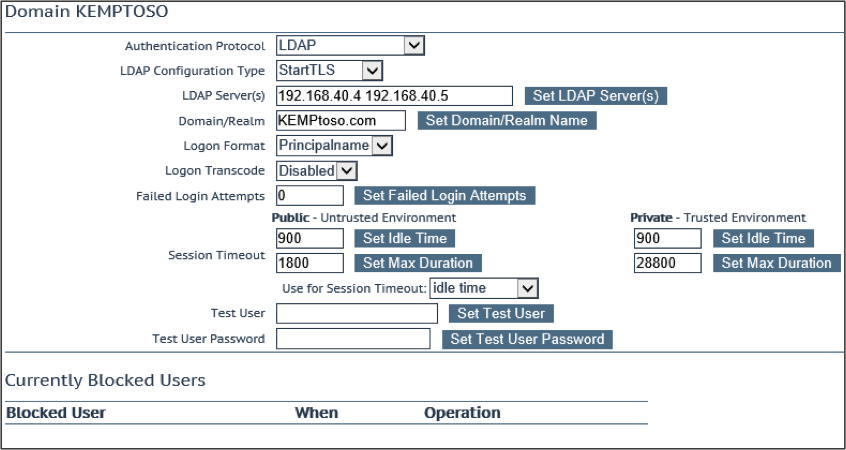
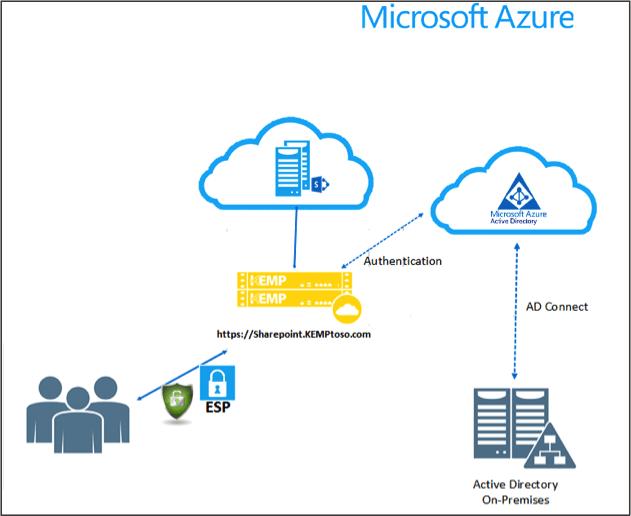
KEMP LoadMaster’s ESP feature allows administrators to create Single Sign On domains to use for pre-authentication against LDAP, RSA, Radius, etc. KEMP’s Edge Security Pack can authenticate users and check group membership prior to allowing access to the backend workload. Now with the introduction of Azure Active Directory Domain Services, KEMP’s Virtual LoadMaster in Azure can authenticate users directly to this service.
Let’s take the Azure Active Directory Domain Services and bring in the Microsoft Azure Active Directory Connect. Synchronize your on-premises Active Directory to Azure with Azure Active Directory Connect and let users authenticate to your workloads in Azure with the same username and password. A nice little bonus is we do all of this without the need to site to site VPN connectivity.
Moving our workloads to the public cloud needs to be transparent to be successful. As more features and functionality are added to the public cloud the more transparent and easier it becomes to migrate these applications.
Useful Links
- Kemp Worldwide
- For more information on KEMP Virtual Load Master for Azure: https://kemptechnologies.com/azure