アプリケーション常時稼働を実現
高度なセキュリティを提供
ハイブリッドクラウド環境に対応できる 次世代ロードバランサーで
アプリケーション配信を最適化し、セキュリティを向上させます。

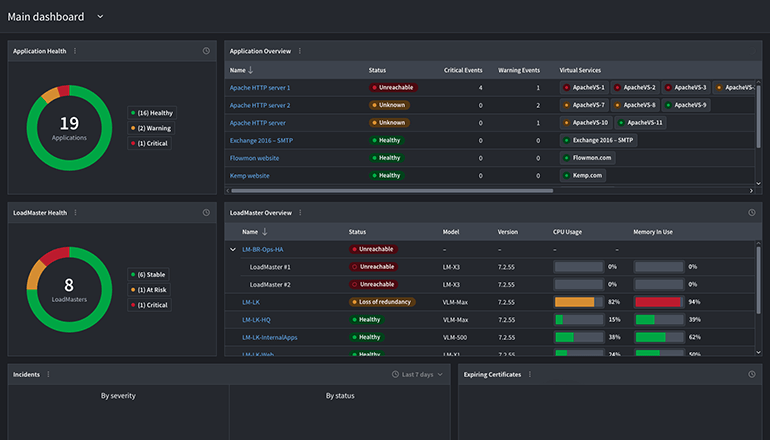
Progress® LoadMaster® 360 は、LoadMaster とアプリケーション配信の管理を効率化し、パフォーマンスを高めます。
LoadMaster でアプリケーション配信を最適化し、セキュリティを強化
Progress® Kemp® LoadMaster® は、業務上重要なアプリケーションや Web サイトに、可用性、スケーラビリティ、パフォーマンス、セキュリティを提供する高性能アプリケーション配信コントローラー (ADC) およびロードバランサーです。LoadMaster ロードバランサーは、SSL オフロード、コンテンツスイッチング、URL 書き換え、圧縮などを備えた高性能なアプリケーション配信ソリューションを、より安全で可用性の高いプラットフォームで提供し、導入と管理が容易です。
LoadMaster の機能「Kemp LoadMaster は、常に高速で信頼性の高いユーザーエクスペリエンスを提供してくれます。」
Shoeb Khan 氏、Audi Volkswagen の CISO

「Microsoft が推奨する Kemp ロードバランサーで、優れたパフォーマンスと高可用性が可能になりました。」
Hossam Hassan Ahmed 氏、ネットワークエンジニア
ソリューションの詳細
証明書のライフサイクル管理
LoadMaster 360 は、運用チームとセキュリティチームに、クラウドとオンプレミスのインフラストラクチャ全体で証明書管理のための単一のコントロールポイントを提供します。
詳細グローバルサーバー負荷分散 (GSLB)
LoadMaster のグローバルサーバー負荷分散 (GSLB) は、使いやすく、費用対効果が高いソリューションです。複数のデータセンターやマルチクラウド環境に高いレジリエンスで対応できます。
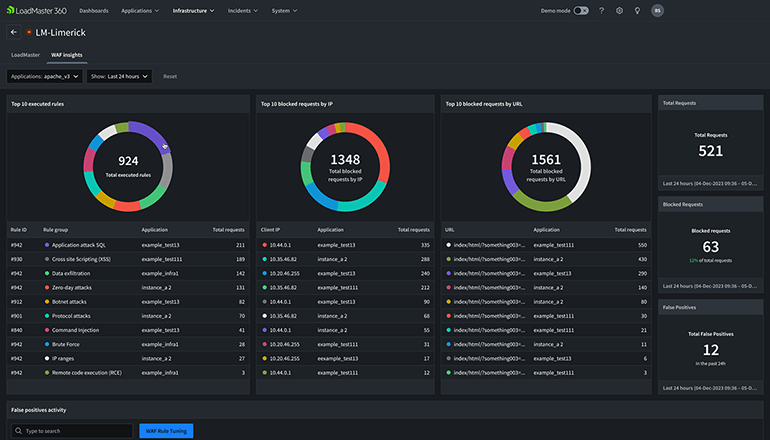
詳細Web アプリケーションファイアウォール (WAF)
LoadMaster の Web アプリケーションファイアウォール (WAF) は、一般的な脆弱性への保護を提供し、アプリケーションのセキュリティを強化します。
詳細Kubernetes の Ingress コントローラー
Kubernetes の Ingress コントローラー は、外部トラフィックを Kubernetes クラスターにルーティングしエンドポイント設定を自動化するシンプルなメカニズムを提供します。
詳細ホワイトペーパー
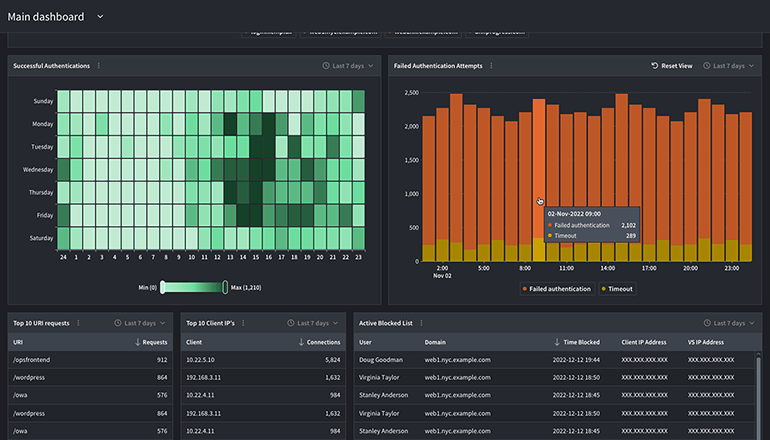
クラウド、SaaS、ハイブリッドなど、非常に複雑化しているインフラストラクチャ環境で、Web アプリケーションをサイバー攻撃から保護することは、組織にとって運用上の重要な必須事項です。サイバー攻撃の手法がますます進化し、脅威が大きくなり続けている状況では、多層防御によって IT の防御を強化する必要があります。ロードバランサーは、この多層化戦略において極めて重要な役割を果たし、アプリケーションのゲートキーパーとして機能します。
ホワイトペーパーをダウンロード
企業が求める常時稼働のアプリケーションエクスペリエンスで絶大な信頼
Gartner Peer Insights を含め、主要な製品レビュー Web サイトで、 業界トップクラスのロードバランサーおよびアプリケーション配信コントローラー (ADC) と評価されています
お客様の声
「現在、組織全体で Kemp LoadMaster を使用しています。高可用性を実現するために必要とするすべてのものが備わっています。」
「長年にわたって Kemp ロードバランサーを使用していますが、非常に高いパフォーマンスで確実に動作します。導入、統合、運用が簡単です。 サポートからの応答は常に迅速です。」
「導入と初期設定は簡単です。この製品は本当に素晴らしく、IT 部門の作業を楽にしてくれます。大変気に入っており、強くお勧めします。」

「使いやすく、直感的なインターフェースを備えています。高可用性構成の作成は非常に簡単でした。LoadMaster のドキュメントは非常に詳細で、サポートスタッフは迅速に対応してくれます。」
世界で100,000を超えるアプリケーションが導入されています
詳細は、下記のプログレスの認定販売パートナーにお問い合わせください。
プログレスへのメールによるお問い合わせ先:sales_japan@progress.com